5 Cybersecurity Careers That Aren't Penetration Testing (And Pay Just as Well)
By Tim O. | CareerPivoting.com | Updated February 2026
Let me guess. You told someone you were thinking about getting into cybersecurity and the first thing they said was, "Oh, so you want to be a hacker?"
No shade to the ethical hackers out there. Penetration testing is a legitimate, well-paying career. But here's what the cybersecurity influencer crowd won't tell you: pentesting is one of the hardest doors to walk through, and it's far from the only one.
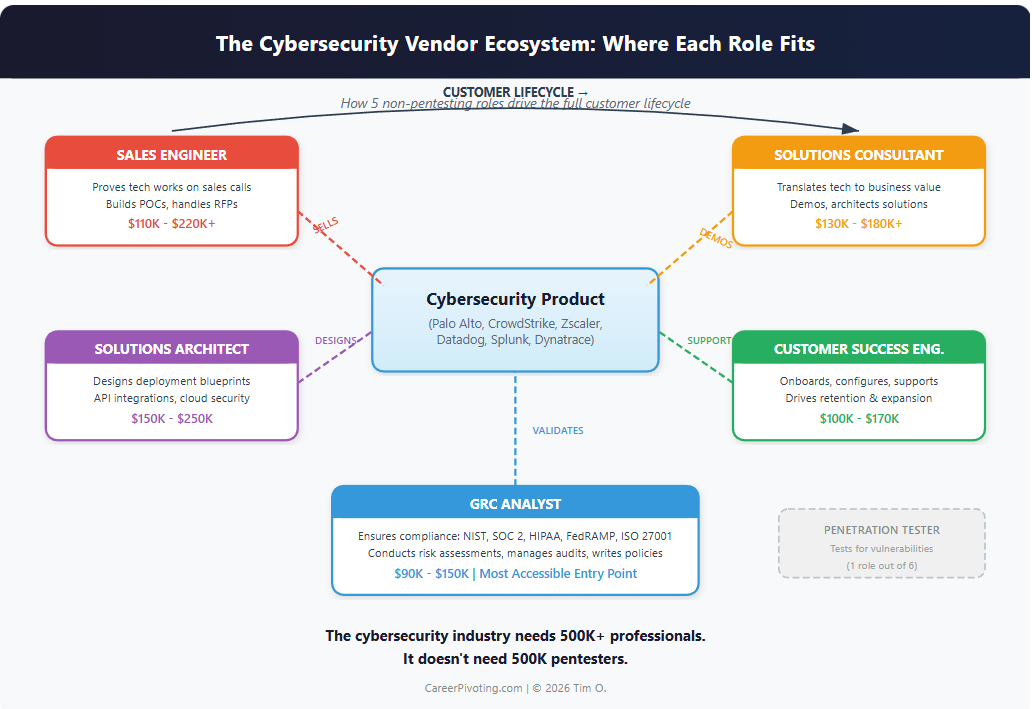
The cybersecurity industry has over 500,000 unfilled positions in the U.S. alone. The vast majority of those openings have nothing to do with breaking into systems. They're about protecting them, selling the tools that protect them, and making sure organizations actually use those tools correctly.
I've spent over a decade in DevSecOps and observability at companies like GitLab, New Relic, and Dynatrace. I've watched people pivot into cybersecurity from HR, from sales, from the military, from teaching. The ones who struggled the most? The ones who thought pentesting was the only path. The ones who thrived? They found roles that matched their actual strengths.
Here are five cybersecurity careers that most people don't know exist. All of them pay six figures at the mid-career level. None of them require you to pass the OSCP or build a home lab at 2 a.m. (though a sandbox mindset never hurts).
Cybersecurity Career Comparison: Pentesting vs. the Five Hidden Roles
Before we break down each role, here's how they stack up against each other and against pentesting. This table is built from 2026 salary data and hiring trends I've observed across the industry.
| Role | Primary Skill | Salary Range (2026) | Entry Ease | Best Background |
|---|---|---|---|---|
| Penetration Tester | Offensive Hacking | $100K - $160K | Difficult | Comp Sci, InfoSec Labs |
| Solutions Consultant | Technical Translation | $130K - $180K+ | Moderate | IT, Networking, Sales |
| GRC Analyst | Policy & Compliance | $90K - $150K | Accessible | Audit, Legal, HR, QA |
| Customer Success Engineer | Relationship Management | $100K - $170K | Moderate | IT Support, Sales Eng. |
| Solutions Architect | Systems Design | $150K - $250K | Advanced | Network Eng., Cloud Infra |
| Sales Engineer | Technical Sales | $110K - $220K+ | Moderate | Sys Admin, IT, Pre-Sales |
Notice something? Four of the five "hidden" roles have a lower entry barrier than pentesting, and three of them match or exceed pentesting salaries at the senior level. The career advice ecosystem just hasn't caught up yet.
Not sure which role fits your personality? Take my 2-minute Career Pivot Quiz to find out if you're a Designer, Translator, or Validator.
1. Why Cybersecurity Solutions Consultant Is the Best Hidden Role
What you actually do: You're the translator. Technical teams build cybersecurity products. Sales teams sell them. You sit in the middle, running product demos, architecting solutions that fit a customer's specific environment, and making sure the deployment actually works.
Why nobody talks about this role: Because the cybersecurity career advice ecosystem is obsessed with "hands-on-keyboard" technical roles. Solutions consulting is technical, but it's also deeply human. You're reading a room, understanding a customer's pain points, and connecting the dots between what a product can do and what a business needs it to do.
Shanikqua Burks, a solutions consultant at Palo Alto Networks, described herself as the "translator between technical teams and internal stakeholders." She started her career in the Army, transitioned to sales engineering, and eventually moved into solutions consulting with the support of Palo Alto Networks' internal mobility programs. She didn't grind through CTF competitions to get there. She leveraged problem-solving skills she'd been sharpening since basic training.
If you're considering a similar military-to-cybersecurity transition, I'll be covering that path in more detail in an upcoming post: How to Pivot Into Cybersecurity From the Military.
The money: Solutions consultants at major cybersecurity vendors like Palo Alto Networks, CrowdStrike, and Zscaler regularly clear $130K-$180K in total compensation. Senior solutions consultants at enterprise accounts can push past $200K with bonuses.
How to get here: A background in IT, networking, or even technical sales can get your foot in the door. Certifications in specific vendor products (like Palo Alto Networks' PCNSE or CrowdStrike's CCFA) carry weight. The real differentiator? Communication skills. If you can explain a Zero Trust architecture to a CISO and a CFO in the same meeting using different language for each, you're built for this.
Tools you'll use daily: Vendor demo environments, Salesforce, Confluence, network diagramming tools (Lucidchart, draw.io), and presentation software. You won't be writing exploit code. You'll be building slide decks that win seven-figure deals.
2. How to Become a GRC Analyst in Cybersecurity (Without Writing Code)
What you actually do: Every organization that handles sensitive data needs to comply with frameworks like NIST 800-53, ISO 27001, SOC 2, HIPAA, PCI-DSS, and GDPR. GRC analysts make sure the company actually does what those frameworks require. You conduct risk assessments, write security policies, manage audit processes, and identify gaps before regulators do.
Why GRC is the most underrated cybersecurity career: GRC gets dismissed as "just paperwork" by the hacker crowd. That's shortsighted. When a company fails a compliance audit, it's not the pentesters who get called into the boardroom. It's the GRC team. This role has direct visibility to leadership, which means it's one of the fastest paths to a CISO seat if that's where you want to end up.
Here's something else people miss: GRC is directly tied to revenue. No SOC 2 report? Enterprise customers won't sign the contract. Failed your FedRAMP authorization? You just lost every federal deal in the pipeline. GRC analysts protect the bottom line in ways that are measurable.
The money: GRC analysts start in the $75K-$95K range. Senior GRC analysts and managers push $120K-$160K. If you specialize in a high-demand framework like FedRAMP or CMMC (Cybersecurity Maturity Model Certification), add another 15-20% to those numbers.
How to get here: This is one of the most accessible entry points in cybersecurity, period. If you have a background in auditing, legal compliance, project management, or even quality assurance, you already have transferable skills. The CISA (Certified Information Systems Auditor) and CISM (Certified Information Security Manager) certifications are your golden tickets. CompTIA Security+ works as a starting point.
The career changer's edge: I've seen former accountants, HR professionals, and paralegals transition into GRC faster than anyone expected. Regulatory frameworks are essentially rule sets, and if your previous career involved interpreting and applying rules to business operations, you're already thinking like a GRC analyst.
Practical application: Want to see what policy enforcement looks like in the real world? Password policies are one of the most common compliance requirements across every major framework. Tools like SafePasswordGenerator.net exist specifically because organizations need to demonstrate they're meeting NIST 800-63B password guidelines. If you can explain why an organization's password policy matters to both the security team and the legal team, you understand the core of GRC work.
3. What Does a Cybersecurity Customer Success Engineer Actually Do?
What you actually do: After a customer buys a cybersecurity product, someone needs to make sure they actually get value from it. That's you. You onboard new customers, help them configure the product for their environment, troubleshoot issues, and serve as their ongoing technical advisor. You're the reason they renew their contract next year.
Why I know this role works for career pivoters: I'm a Senior Customer Success Engineer at Dynatrace. I got here after years in DevSecOps, but I've worked alongside customer success engineers who came from completely different backgrounds. What they all had in common was the ability to listen to a customer's problem, understand their technical environment well enough to diagnose it, and communicate a solution clearly.
The observability and cybersecurity spaces overlap significantly here. Platforms like Datadog, Splunk, Elastic, Grafana, and Dynatrace are used by security operations teams daily. Customer success engineers working with these platforms are already operating in the cybersecurity ecosystem, whether they realize it or not.
The money: Customer success engineers in cybersecurity and observability typically earn $100K-$140K base salary, with total compensation (including bonuses tied to retention and expansion metrics) reaching $150K-$175K at senior levels.
How to get here: Technical support or help desk experience is the most common stepping stone. If you've worked in IT support and you're frustrated by the ceiling, customer success engineering is the logical next move. You'll need to develop product expertise (vendors often provide extensive training, and companies like Palo Alto Networks will even ship you hardware to build a home lab), but the core skill is the one you already have: solving problems for people who are stuck.
The underrated advantage: Customer success roles give you exposure to dozens of different customer environments. In two years, you'll have seen more real-world security architectures than most pentesters see in five. That breadth of experience makes you incredibly valuable if you later want to move into solutions consulting, product management, or even start your own consulting practice.
4. Cybersecurity Solutions Architect: The Quiet $200K Career
What you actually do: Solutions architects design the technical blueprint for how cybersecurity products integrate into a customer's existing infrastructure. Where a solutions consultant might demo the product and explain its capabilities, the solutions architect goes deeper. You're designing network diagrams, mapping out API integrations, planning cloud security deployments across AWS, Azure, and GCP, and ensuring the solution scales.
Why this is the "quiet $200K job": Solutions architects don't get the social media attention that ethical hackers do. They're not posting writeups on HackTheBox. But they're some of the highest-paid individual contributors in the cybersecurity vendor space. Companies like Palo Alto Networks, Fortinet, CrowdStrike, and Cisco pay top dollar for architects who can design enterprise-grade deployments.
The money: Mid-career solutions architects in cybersecurity earn $150K-$200K in total compensation. Staff and principal architects at major vendors or large enterprises can exceed $250K.
How to get here: This is typically a mid-career role. Most solutions architects spent 5-8 years in network engineering, systems administration, or cloud infrastructure before making the move. If you're currently a network admin or cloud engineer, cybersecurity solutions architecture is one of the most natural and lucrative pivots available. AWS Security Specialty, Azure Security Engineer (AZ-500), and GCP Professional Cloud Security Engineer certifications will strengthen your positioning, alongside vendor-specific certs.
The progression: Burks' own career path at Palo Alto Networks illustrates this perfectly. She started as a senior solutions architect before transitioning to solutions consultant. Both roles are deeply technical, but they emphasize different skills. Architecture is about depth. Consulting is about breadth. Understanding how they connect gives you options most cybersecurity professionals never realize they have.
5. Why Cybersecurity Sales Engineer Is a Career Accelerator
What you actually do: Sales engineers are the technical half of the sales team. You join sales calls to answer the hard questions, build proof-of-concept environments, respond to RFPs (Requests for Proposal), and demonstrate how the product solves specific technical problems. You're closing deals by proving the technology works.
Why this role is a career accelerator: Sales engineering is one of the few roles where technical skills and business impact intersect directly. Every deal you help close has a revenue number attached to it. That visibility translates into faster promotions, larger bonuses, and more leverage when negotiating your next role.
The money: Base salaries for cybersecurity sales engineers range from $110K-$150K. Total compensation, including commission and bonuses, often pushes $160K-$220K. Top performers at enterprise cybersecurity companies like CrowdStrike, Palo Alto Networks, and Zscaler can earn $250K+.
How to get here: Former systems administrators, network engineers, and even technical support professionals make strong sales engineers. The technical bar is real but manageable. You don't need to be the world's foremost expert on the product. You need to know it well enough to handle 90% of customer questions live, and know when to bring in a specialist for the other 10%. If you're the person on your current team who always ends up explaining technical concepts to non-technical people, this is your sign.
What makes cybersecurity sales engineering different: The buyer sophistication is higher than in most tech sales. CISOs and security architects ask pointed questions. They've been burned by vendors who overpromise. Your credibility is your currency. If you can earn their trust with honest, technically accurate answers, you'll build a career that compounds.
The Myth That's Costing You Time (and Money)
The cybersecurity career advice industry has a gatekeeping problem. Too many influencers and bootcamp marketers push the narrative that penetration testing is the "real" cybersecurity career and everything else is a consolation prize.
That's wrong, and it's expensive. People spend thousands on OSCP prep courses and months grinding through CTF challenges only to discover they don't actually enjoy breaking things. They enjoy understanding how things work and helping organizations work better. That's solutions consulting. That's GRC. That's customer success. That's architecture. That's sales engineering.
The cybersecurity industry needs 500,000+ professionals. It doesn't need 500,000 pentesters. It needs people who can translate, comply, support, design, and sell.
Figure out which of those verbs sounds like you, and go build a career around it.
Frequently Asked Questions
Do I need a degree to become a GRC Analyst?
No. While a bachelor's degree in information technology, business, or a related field can help, many GRC analysts break in with certifications and relevant work experience. CompTIA Security+ is the most common starting point. The CISA and CISM certifications carry the most weight with hiring managers. If you have a background in auditing, legal compliance, or quality assurance, your existing experience counts more than a specific degree.
What's the difference between a Sales Engineer and a Solutions Consultant in cybersecurity?
The roles overlap, and titles vary by company. Generally, a sales engineer is more tightly integrated with the sales team and focused on the pre-sale technical validation (demos, POCs, RFP responses). A solutions consultant may also handle post-sale technical guidance and has broader responsibilities around solution design. At some companies like Palo Alto Networks, these are distinct roles with different compensation structures. At others, they're the same job with different titles. When evaluating job postings, focus on the responsibilities listed, not the title.
Can I transition into cybersecurity from a non-technical background?
Yes, particularly into GRC, customer success, and certain sales engineering roles. The key is identifying your transferable skills. Accountants and auditors have a natural path to GRC. Teachers and trainers fit well into security awareness roles. Project managers can move into security program management. Sales professionals with technical curiosity make strong sales engineers. The common thread isn't technical depth; it's the ability to learn quickly and communicate clearly.
How long does it typically take to pivot into one of these cybersecurity careers?
It depends on your starting point, but most career changers I've worked with or observed made the transition in 6-18 months. The fastest path usually involves getting a foundational certification (Security+ or equivalent), building product knowledge through vendor training programs, and networking with people already in the role you're targeting. LinkedIn is underrated for this. Most cybersecurity professionals are willing to have a 15-minute conversation with someone genuinely interested in the field.
Which of these five roles is best for someone with no IT experience?
GRC Analyst is the most accessible starting point for people without an IT background. The work centers on policy, compliance, and risk assessment rather than hands-on technical operations. If you can read a regulatory framework, conduct an assessment against it, and write a clear report on the gaps, you have the core skills. From there, you can layer on technical knowledge over time and expand into other roles.
Tim O. is a Senior Engineer with 10+ years in DevSecOps. He writes about career transitions at CareerPivoting.com.
Last updated: February 2026